- A new LinkedIn phishing scheme uses fake “Private Shared Document" to target users.
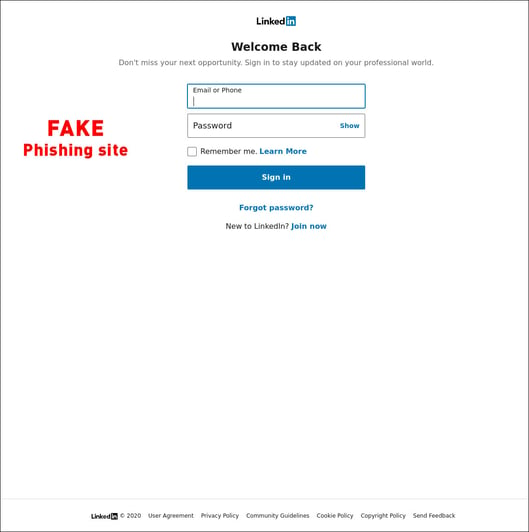
- Malicious PDF file direct victims to a LinkedIn-themed credential skimming page
- After compromise, same phishing message is sent to all of the victimized account’s contacts, and the cycle repeats.

The PDF then directs victims to LinkedIn-themed credential skimming pages. The phishing pages were hosted on a variety of domains, that the actor would alternate between.
If an individual enters their LinkedIn credentials on the page, the malicious actor then compromises that account and would send the same phishing message out to all of the victimized account’s contacts, and the cycle would repeat.
According to the researcher’s report, the skimming page would simply send the users back to LinkedIn after they entered their credentials. It would not try to serve up any other files to the victim. It is also important to note that aside from the phishing link, the PDFs used to direct individuals to the skimming page did not attempt to install anything on the victim's machine.
While the only activity reported for this LinkedIn phishing campaign was the compromising of account credentials, these compromised accounts could be the first stage for a variety of other, potentially more damaging attacks. They include:
- Credential Reuse: If the victims had reused their LinkedIn credentials on any other systems, the actor could use these compromised credentials on other systems (i.e., common email or banking services)
- Business Communication Compromise (BCC): The actor could use these compromised accounts (specifically any belonging to executives) to convince co-workers and employees of the victimized account to transfer funds or sensitive information for seemingly business purposes.
- Malware Distribution: The actor could try to use the accounts to deliver malware to individuals in the victimized account’s network as message attachments.
- Brand Damage: If the victimized accounts were associated with any public-facing resources (like an official company LinkedIn page), the actor could attempt to access those resources as well and post materials that could damage the company’s public image.
This LinkedIn phishing scam, along with similar attack opportunities, demonstrate how compromised personal accounts can potentially lead to severe impacts not only for the victimized individuals but to their network and the companies that employ them. LinkedIn messages, along with other social media communications apps such as Twitter DMs and WhatsApp messages, have become major social engineering targets that go far beyond the email scams most people are familiar with.
And yet, while these social media messaging accounts are part of an attack surface for companies that provide some risk, as shown above, most organizations still have not implemented ways for helping to secure them.
Whitepaper: Learn how to protect your assets.
Sure, one can easily report LinkedIn phishing emails they received by forwarding them to phishing@linkedin.com. Users can also report suspicious messages they believe are phishing attempts through the “More” option in-app. However, this process still relies on the user’s intuition and their capability to recognize whether a message is a phishing attempt or not. This is not enough.
At SafeGuard Cyber, we provide businesses with the ability to secure the social media messaging accounts of their key employees and protect them against phishing attacks and other forms of digital threats without infringing on their privacy. We allow security teams to review risk (and compliance) events without exposing the content of an individual’s communications.
If you want to learn more about how our security solution can protect your brand and employees from phishing attacks on LinkedIn and other channels, feel free to contact us and request a demo today.

.jpg)