Complimentary Report: How to Respond to the 2023 Cyberthreat Landscape
Security and risk management leaders must refine their strategies to identify and better adapt to the most important cyberthreat trends rather than allocating resources to overhyped or hypothetical attack scenarios.
The report addresses three threat categories:
- Top threats. Threats that organizations are highly aware of and remain relevant year after year as a result of underlying changes.
- High-momentum threats. Threats that are growing, but for which awareness is not yet on par with that associated with the top threats.
- Uncertain threats. There is an infinite list of new and potential threats. The main question for this category is to determine whether the organization needs to address, postpone or ignore these “low signal” threats, which can be emerging and dangerous, or overhyped and a distraction.
SafeGuard Cyber: We Believe What's Old is New
The report states, "For the last decade or so, the same threats remain as the top trends: malware/ransomware, phishing and credential abuse."
We feel the evolution of phishing stand out as it now "involves using multiple channels, predominantly email, but attackers these days are also utilizing collaboration platforms, social media, text messaging (smishing), voice messaging (vishing) and even quick response (QR) codes to gather information."
KEY TAKEAWAY
Microtrends in phishing techniques mean organizations will need to adapt to higher volumes of phishing attacks coming from multiple channels.
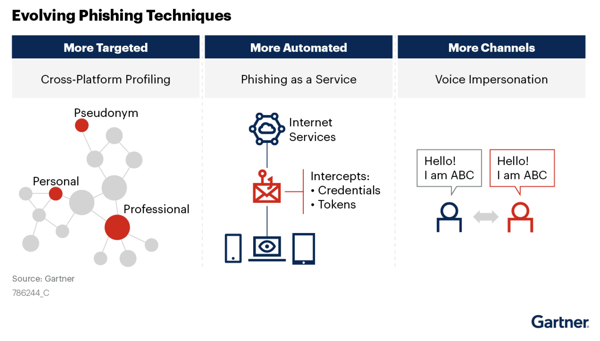
Holistic visibility across multiple business communication channels is the highest priority.
SafeGuard Cyber is proud to be able to provide this complimentary report as a planning resources for security leaders.
Get the complimentary research today!
Disclaimer: GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved. Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, express or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
Access the Report
Expert Insights on the Cloud Workplace
Stay up-to-date on security and compliance risks that occur in collaboration, mobile chat, conferencing, social media, and email. Learn from experts about how SafeGuard Cyber addresses important enterprise initiatives like zero trust, remote work, digital transformation, and regulatory compliance.