Extend Zero Trust Principles to Business Communications
Extend Zero Trust principles from network and data systems to your cloud communications channels. Gain defense-in-depth to stop risks like insider threats and impersonation and prevent lateral movement from social engineering attacks that compromise employee accounts.
of security decision-makers say that Zero Trust is critical to their organization’s success
of respondents citing high-profile ransomware incidents as the top motivator for deploying Zero Trust
reduction in the average cost of a data breach with a Zero Trust strategy
Source: 12 Illuminating Zero Trust Statistics and Trends in 2022
In cloud-native or hybrid network infrastructures, everything is accessible from data centers and the cloud. VPN login credentials can easily fall into the wrong hands and wreak havoc on the systems of organizations, as with the Colonial Pipeline incident.

Zero Trust solutions can help mitigate the danger by providing:
Sensitive data protection
Compliance audit support
Reduced breach risk and detection time
Network traffic visibility
Better cloud environment control
Microsegmentation
Data Breaches: Worse Every Year
2022
- The British police arrested several alleged members of the Lapsus$ hacking group due to a slew of data breaches on top global companies – Microsoft, Samsung, Ubisoft, Nvidia, and Okta. The group gained access to and utilized communication channels like Slack and Teams.
- Scammers created a deepfake of Binance CCO Patrick Hillmann using previous TV appearances and interviews to create a hologram “refined enough to fool [and scam] several highly intelligent crypto community members.”
2021
- A stolen Slack authentication cookie enabled bad actors to infiltrate the EA Games’ network, stealing 780Gb worth of data, including source codes, to two of the company’s multi-billion dollar franchises.
2020
- Cyberark discovered a vulnerability in Microsoft Teams. The attack utilized a weaponized GIF which, when viewed, began stealing data.
- The following month, foreign spies were discovered targeting American companies and individuals through Zoom and other video conferencing platforms.
- A few more months later, researchers discovered a vulnerability in Slack’s create snippet feature, which allowed attackers to smuggle malware and other malicious files into the environment.

Prevent attackers from moving laterally within your environment.

Secure Business Communication Channels
Close gaps in your security posture with deep visibility into business communications across 30 channels in both corporate and personal assets. Risk analytics for language-based attacks enable teams to scrutinize suspicious human behavior revealed in communication patterns. Detect and correlate risk events across channels, to disrupt attacks earlier and rapidly reduce investigation time.
Identify the Context and Intent of Communications
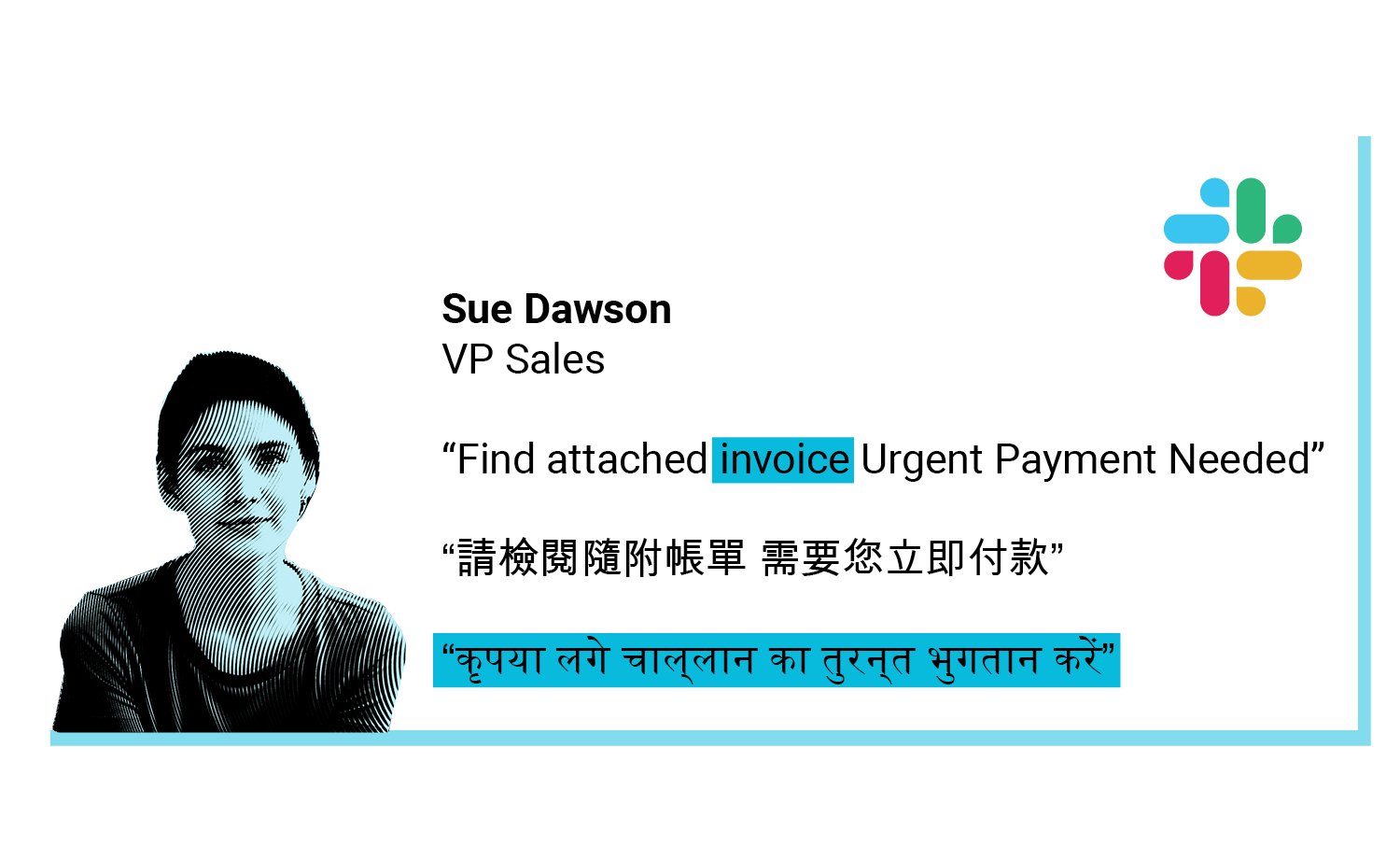
With Contextual Analysis, teams move beyond just metadata analysis to understand the intent behind workspace communications. Our patented Natural Language Understanding technology and Social Engineering Detection capabilities help security teams determine HOW and WHY suspicious communications are taking place.
How Our Customers Prevent Malware Intrusion, Impersonation, and Fraud
With SafeGuard Cyber they can now detect social engineering in 50+ languages, prevent malware and ransomware from propagating the business, and reduce risk to the organizations in human communications.
The company had to pay a third-party agency to manually search, review, and process takedown requests -- a costly and time-intensive process. The organization felt it was still missing risks and takedowns were taking too long and were difficult to track. SafeGuard Cyber dramatically reduced the organization’s brand protection costs and resources.
Adopt a Zero Trust Model for Secure Communications
Related Content
Safeguard Modern Communications
Ready to take the next step?
Expert Insights on the Cloud Workplace
Stay up-to-date on security and compliance risks that occur in collaboration, mobile chat, conferencing, social media, and email. Learn from experts about how SafeGuard Cyber addresses important enterprise initiatives like zero trust, remote work, digital transformation, and regulatory compliance.






.png)





